Security Flaws in UPnP protocol put 50 million devices at risk

A Security Flaw in Universal Plug & Play (UPnP) are exposing more than 50 millions of computers, printers and storage drives to attack by hackers remotely. Rapid7 said Tuesday in a research paper, that problem lies in routers and other networking equipment that use a commonly employed standard known as Universal Plug and Play or UPnP. UPnP allows networked devices to discover each other and automatically establish working configurations that enable data sharing, media streaming, media playback control and other services. In one common scenario a file-sharing application running on a computer can tell a router via UPnP...
nCircle patches PureCloud vulnerability scanner on Vulnerability-Lab report

The Vulnerability-Laboratory Research Team discovered persistent and client side POST Injection web vulnerability in the nCircle PureCloud (cloud-based) Vulnerability Scanner Application. The vulnerability allows an attacker to inject own malicious script code in the vulnerable module on application side. Benjamin K.M. from Vulnerability-Laboratory provide more technical details about these flaws, the first vulnerability is located in the Scan Now > Scan Type > Perimeter Scan > Scan section when processing to request via the `Scan Specific Devices - [Add Devices]` module and the bound vulnerable formErrorContent...
SSH Backdoor accounts in multiple Barracuda Products

Firewall, VPN and spam filtering products from Barracuda Networks contains hidden hard coded backdoor ed SSH accounts, that allow any hacker to remotely log in and root access sensitive information. According to an advisory published by Stefan Viehböck of SEC Consult Vulnerability Lab reported the vulnerabilities in default firewall configuration and default user accounts on the unit. Barracuda were informed of the vulnerabilities at the end of November. All Barracuda Networks appliances with the exception of the Barracuda Backup Server, Barracuda Firewall, and Barracuda NG Firewall are potentially affected i.e Barracuda...
Hundreds of SSH Private Keys exposed via GitHub Search

GitHub is a source code repository which lets developers work on programs together as a team, even when they are in different locations. Each repository on the site is a public folder designed to hold the software code that a developer is working on. This Tuesday GitHub announced a major upgrades to the site's search engine, "Finding great code on GitHub just got a whole lot easier,". Yesterday few twitter users pointed out that there is no shortage of embedded private SSH keys and passwords that can easily be found via GitHub new feature. If you upload security information (keys/passwords etc) to a public repository, new search feature...
Take down of fifth most widespread 'Virut Botnet'

NASK the domain registrar that operates the “.pl” Polish top-level domain registry has seized multiple domains used for cyber crime activities by spreading Waledac malware distributed by the Virut botnet. According to Poland’s Computer Emergency Response Team, Virut was first detected in 2006 and became a serious threat with an estimated size of more than 300,000 compromised computers. NASK said that on Thursday it began assuming control over 23 .pl domains that were being used to operate the Virut network. Virut was responsible for 5.5% of infections in Q3 2012, making it the fifth most widespread threat of the time. They...
Shylock banking malware spreads via Skype

The banking Trojan known as Shylock has been updated with new functionality, including the ability to spread over Skype. The program was discovered in 2011 that steals online banking credentials and other financial information from infected computers. Shylock, named after a character from Shakespeare's "The Merchant of Venice". Shylock is one of the most advanced Trojans currently being used in attacks against home banking systems. The code is constantly being updated and new features are added regularly. According to security researchers from CSIS Security Group, the Skype infection is based on...
Why I decided to uninstall Microsoft Security Essentials Antivirus?
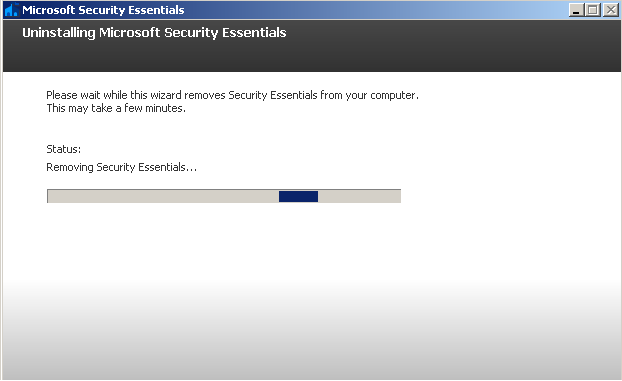
Today I decided to remove Microsoft Security Essentials Antivirus from my system because Security Essentials failed another certification test by independent testing lab, AV-Test Institute. Microsoft's Security Essentials antivirus for Windows XP, Vista, and Windows 7 is a free add-on to Windows Defender, which blocks adware and spyware on Windows. In its review, AV-Test revealed that 22 of the 25 programs that were tested passed the test, but Security Essentials came up short. The lab tested all programs across three areas: protection, repair ability and usability of the whole computer based on the impact of the software. "We...
The use of passwords in a technological evolution

Every day we read about an incredible number of successful attacks and data breaches that exploited leak of authentication mechanisms practically in every sector. Often also critical control system are exposed on line protected only by a weak password, in many cases the default one of factory settings, wrong behavior related to the human component and absence of input validation makes many applications vulnerable to external attacks. Today I desire to focus the attention of a report published by the consulting firm's Deloitte titled “Technology, Media & Telecommunications Predictions 2013” that provide a series of technology predictions,...
Malware Infects US Power Plants through USB Drives

The US Department of Homeland Security’s Cyber Emergency Response Team has released a report, which stated that two American electrical power plants were compromised late last year and has identified a number of glaring electronic vulnerabilities. Some unknown malware infected two power plants control systems using unprotected USB drives as an attack vector. The tainted USB drive came in contact with a handful of machines at the power generation facility and investigators found sophisticated malware on two engineering workstations critical to the operation of the control environment. The report did not say if the computers did...
Cisco Linksys routers vulnerable to remote zero-day exploit

A zero-day vulnerability has been discovered in popular Cisco Linksys routers that allows hackers to gain remote root access. Security vendor DefenseCode discovered the flaw and reported it to Cisco months ago and a fix is already on the way. According to Cisco, more than 70 million Linksys routers sold globally. This exploit was successfully tested against a Linksys model WRT54GL router by researchers at security firm DefenseCode who claimed that the latest Linksys firmware 4.30.14 and all previous versions are still vulnerable. It took the team only 12 days to develop an exploit that could be used by hackers to take control...
Oracle Patches Java Zero Day Vulnerability

Oracle delivered an unusual emergency patch to Java's critical Zero Day vulnerability on Sunday to fix a malicious bug that allowed hackers access to users web browsers. Exploits for the previously undisclosed flaw were being hosted in a number of exploit kits and attacks have already been seen in the wild dropping ransomware and assorted other malware. Security Alert CVE-2013-0422 include two vulnerabilities that are remotely executable. Oracle confirmed that the flaws were only present in Java 7 versions and did not impact Java on servers, Java desktop applications, or embedded Java. Java is used in 3 billion machines,...
Operation Red October : Cyber Espionage campaign against many Governments

A new sensational discovered has been announced by Kaspersky Lab’s Global Research & Analysis Team result of an investigation after several attacks hit computer networks of various international diplomatic service agencies. A new large scale cyber-espionage operation has been discovered, named Red October, name inspired by famous novel The Hunt For The Red October (ROCRA) and chosen because the investigation started last October. The campaign hit hundreds of machines belonging to following categories: Government Diplomatic / embassies Research institutions Trade and commerce Nuclear / energy research Oil and gas companies Aerospace Military The...
Under the hood of recent DDoS Attack on U.S. Banks

Incapsula security study reveals how a simple neglect in managing the administrative password of a small UK site was quickly exploited by Botnet shepherds operating obscurely out of Turkey to hurl large amounts of traffic at American banks. If you've been following the news, you are probably aware of a wave of DDoS attacks that recently hit several major U.S. banks. Izz ad-Din al-Qassam, a hacker group that claimed responsibility for these attacks, declared them to be a retaliation for an anti-Islam video that mocked the Prophet Muhammad and a part of the on-going “Operation Ababil.” As the reports of the attack started...
5 Checks You Must Run To Ensure Your Network Is Secure

Twenty-four hours a day, seven days a week, 365 days each year – it’s happening. Whether you are awake or asleep, in a meeting or on vacation, they are out there probing your network, looking for a way in. A way to exploit you; a way to steal your data, a place to store illegal content, a website they can deface, or any of a hundred other ways to mess with you for the simple joy of it all. And they can do this with relative ease, even in an automated fashion, with simple tools that are readily available to all. I’m talking about network scanners. The bad guys use them all day every day to assess networks around the world because a network...
Warm up your keyboard for Facebook Hacker Cup 2013

Dear Hackers, Warm up your keyboards! Because Facebook open Registration for third Hacker Cup 2013, an annual worldwide programming competition where hackers compete against each other for fame, fortune, glory and a shot at the title of world champion, with $5,000 top prize. The qualification round begins on January 25th. So Participate and enhance your programming competency. The dates have been set for Facebook Hacker Cup 2013Jan 7 — Jan 27 — Registration Jan 25 — Jan 27 — Online Qualification Round Feb 2 — Online Elimination Round 1 Feb 9 — Online Elimination Round 2 Feb 16 — Online Elimination Round 3 March 22 -23 — Onsite Finals at...
SkypeHide to Send secret messages into silence of Skype Calls

Polish Researchers have discovered a clever way to send secret messages during a phone call on Skype. We know that, by default skype calls use 256-bit advanced encryption, but researchers find that is not enough. So they find out this new way to communicate messages more secretly by using silence. Mazurczyk, Maciej Karaś and Krzysztof Szczypiorski analysed Skype data traffic during calls and discovered that there is a way in Skype silence, where rather than sending no data between spoken words, Skype sends 70-bit-long data packets instead of the 130-bit ones that carry speech. So by taking advantage of this they hijacks these silence...
Password reset Vulnerability in Facebook Employees Secure Files Transfer service
Many be many of you are not aware about this, but Facebook having a Secure Files Transfer service for their Employees at https://files.fb.com and Hacker reported a very critical password reset vulnerability. Nir Goldshlager, a researcher told 'The Hacker News' that how he defeat Facebook's Secure Files Transfer service and help Facebook by reporting them about this issue in a responsible non-disclosure way till patch. After analyzing the site, he found that the script Facebook is using is actually "Accellion Secure File Sharing Service" script and so next he download the demo version of service from Accellion...
Latest Internet Explorer zero-day linked to Elderwood Project

Last week we have seen ongoing attacks was exploiting a vulnerability in Internet Explorer 6, Internet Explorer 7, and Internet Explorer 8 that came to light after the Council on Foreign Relations website was hacked and was hosting the code. Symantec has linked exploits to the group responsible for a spate of recent espionage attacks Dubbed the "Elderwood Project". In May 2012, Amnesty International’s Hong Kong website was compromised & used to serve up a malicious SWF file that exploited CVE-2012-1875, a vulnerability affecting Internet Explorer. A few months later in Sep 2012, the same group behind that attack was responsible...
Indian Government Wiretapping and started BlackBerry interception

According to a report, All major Indian telecom companies, including Bharti Airtel, Vodafone India and Tata Tele services, have agreed to share real-time interception of BlackBerry calls and data services on their networks with Security agencies to meet the December 31 deadline fixed by the Indian government . Research In Motion (RIM), the manufacturer of BlackBerry, has been directed to provide the resolution and web-browsing needs of the BlackBerry Internet Services. This is to be done in discussion with concerned service providers and law interception organisations. Earlier in 2011, the government set the deadline for RIM to come...
Zero-Day Vulnerability in Symantec PGP Whole Disk Encryption
Symantec product PGP Whole Disk Encryption which is used to encrypt all the contents on the disk on a block-by-block basis having Zero-Day Vulnerability, according to a pastebin note. Note was posted on 25th Dec by Nikita Tarakanov, claiming that pgpwded.sys kernel driver distributed with Symantec PGP Desktop contains an arbitrary memory overwrite vulnerability. Affected version of software is Symantec PGP Desktop 10.2.0 Build 2599 (up-to date). Through a blog post, Symantec confirmed that its a potential issue, but it cannot easily be exploited. Vulnerability is limit systems running...
What is phishing and how to be safe
from phishing ?22:48 Posted by Bimal
bhattarai
What is Phishing ?
Phishing is one of the type of hacking . It is a method of acquiring sensitive information such as username, password, bank information etc. Phishing pagecould be saif as an duplicate page of real one. Its look exactly similar as the real page.But when user enter sensitive information on such phishing page his information is send to the E-mail address provided in the phishing page or you can say the one who created that phishing page. Phishing page is mostly send via mail. Target of phishing are mostly social networking sites like facebook, orkut etc. Also Banks website to acquirecredit card details,website like yahoo, gmail are also target of phishing.
Example of Phishing scams:
- Email asking you to login to your locked account to unlock it.
- Email carrying a Link to sites like Facebook,yahoo etc and asking you to Login.
- Emails containing some Information of your Interest and asking you to Login toYour Account.
How to be safe from phishing ?
- Never login to any of your account through link provided in the Email.
- Go to real website dont click on any link posted anywhere. such as link posted on your facebook wall by friend or link provided in comments or link to ceratin website on any blog.
- Check the URL of website before entering any sensitive information. Because the URL of phishing page is not same as the URL of real one.
- Real gmail page looks like gmail.com while phishing looks different somthing likegmail.anything.com
What is Encryption?
Encryption is a method or a technique used to encode a message so that it can’t be read by a normal user/person. Its an art of secret writing, It can also be defined as converting information from plain text using an algorithm or a cipher to make it unreadable, So that the converted information can only be read by the person who is having the special knowledge. The process of encoding is known as Encryption and its reverse process i.e. decoding it is known as Decryption. Encryption is very useful when it comes to protecting your confidential data from being stolen. It is helpful when data is transmitted over the network, it safe guards you data from sniffers. When data is needed to be encrypted over a network, SSL Protocol is used for encryption purpose. SSL stands for SecureSocket Layer.
Types of Encryptions
Symmetrical Key : This type of encryption is also know as Shared Key Secret. In symmetrical encryption, the key which is used in the process of encryption, that same key is also used in the process of decryption. If two parties want to exchange the encrypted data securely, both of them should have the same copy of symmetric key.
Asymmetrical Key : This type of encryption is also know as Public Key. In this type of encryption, keys are generated in pairs, public key and private key. In asymmetrical encryption key used to encipher is different from the key used to decipher. Therefore the two partners have two different keys, one is made public and other one is made private. Let’s take up an example to understand the concept in an easy way.
Suppose, John wants to send a message to Mike, he just ciphers the message with the public key and sends it to Mike. Since Mike is having the secret key, he can and decipher the message and read its content.

No comments:
Post a Comment